- I recommend the Pixel 9 to most people looking to upgrade - especially while it's $250 off
- Google's viral research assistant just got its own app - here's how it can help you
- Sony will give you a free 55-inch 4K TV right now - but this is the last day to qualify
- I've used virtually every Linux distro, but this one has a fresh perspective
- The 7 gadgets I never travel without (and why they make such a big difference)
Network Visibility Module and Zeek Detections in Secure Network Analytics
Secure Network Analytics version 7.5.2 has been released, offering exciting new features such as the Network Visibility Module (NVM) and Zeek detections. We are expanding our detections across existing and new sources, and our detections engine now ingests NVM telemetry and Zeek logs, introducing nine new alerts prominently displayed in Analytics. These alerts are also aligned with the widely recognized MITRE ATT&CK framework.
By integrating a more diverse range of telemetry sources, Secure Network Analytics significantly enhances network visibility and provides deeper insights into network activities. This release and its detections represent an advanced approach to broadening detection sources and capabilities. Users utilizing the Data Store architecture with Analytics enabled can upgrade to version 7.5.2 to immediately access these new capabilities.
The Secure Network Analytics version 7.5.2 software updates can be downloaded from Cisco Software Central.
New Network Visibility Module (NVM) Alerts
Network Visibility Module is a component of Cisco Secure Client that records and reports on network activity from an endpoint device and ties in endpoint style information with those network details. If you are used to collecting NetFlow or IPFIX in your environment, the Network Visibility Module will provide the same details about a network connection, but will also include things like hostname, process name, user information, operating system, interface details, and more. This helps speed up investigations and provides additional context about who and what host took an action on the network. The detections engine processes the Network Visibility Module telemetry and alerts on four new detections.
You can check out the Network Visibility Module Configuration Guide.
Network Visibility Module (NVM) Alert Names and Descriptions
Potential Gamaredon C2 Callout
A command line utility was used to contact a URL associated with the command-and-control servers of a threat actor known as Gamaredon. Gamaredon (also known as Armageddon, Primitive Bear, and ACTINIUM) is an APT active since 2013 known to leverage spearphishing to infect victims with custom malware.
Suspicious Curl Behavior
The system utility curl exhibited suspicious behavior that may be indicative of exploitation of CVE-2023-38545.
Suspicious MSHTA Activity
The built-in Windows application MSHTA.exe was executed interactively by a non-system user and utilized to make a network connection. While typically legitimate when run automatically by the system, it is also known to be utilized by threat actors including Advanced Persistent Threats (APTs).
Suspicious Process Path
A process was executed on an endpoint from a directory that should not have executables.
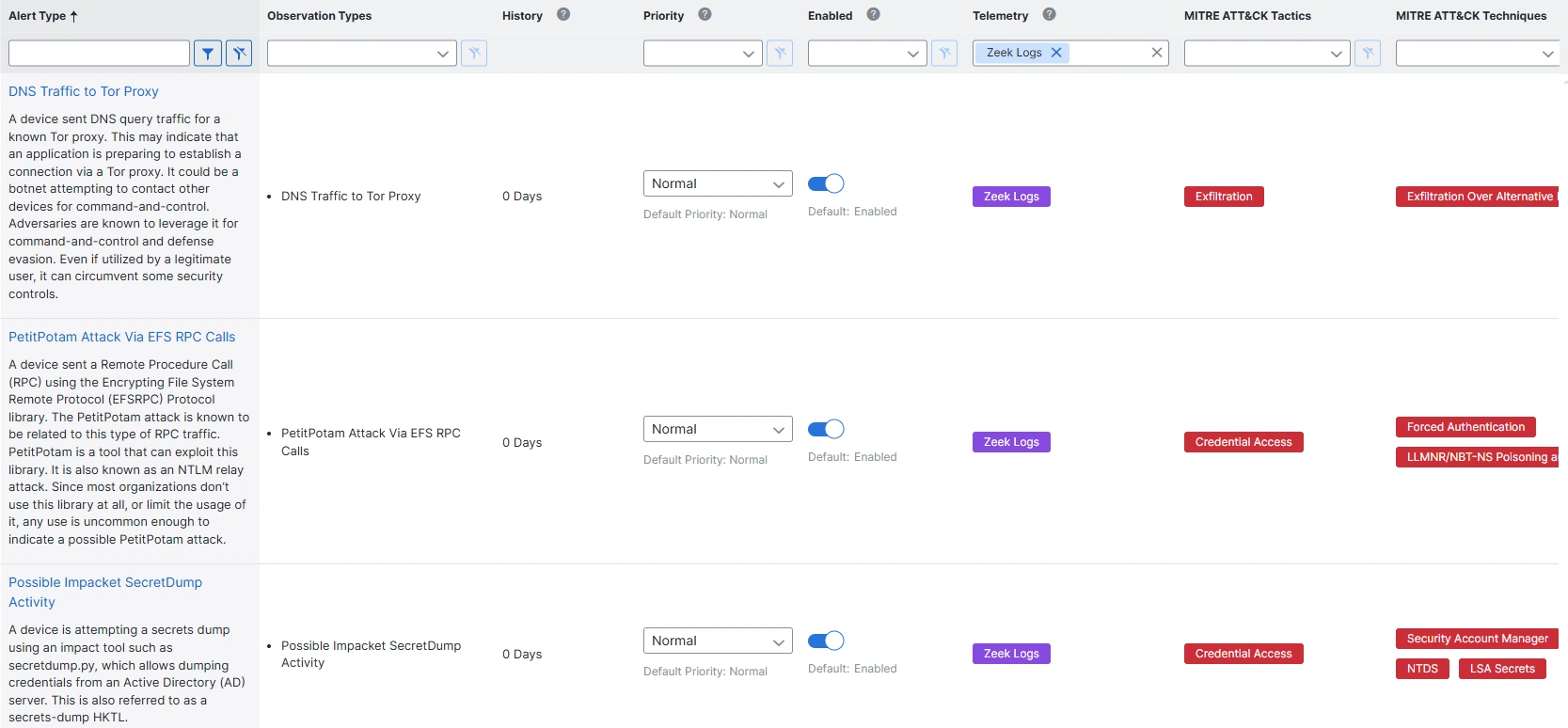
New Zeek Alerts
Zeek is a popular, free, and open-source network traffic analysis tool. It monitors and inspects traffic and generates log files of witnessed activity. Those Zeek log files can be sent to Secure Network Analytics as a telemetry source. The detections engine reads the Zeek logs and alerts on five new detections.
Check out the Zeek Configuration Guide.
Zeek Alert Names and Descriptions
DNS Traffic to Tor Proxy
A device sent DNS query traffic for a known Tor proxy. This may indicate that an application is preparing to establish a connection via a Tor proxy. It could be a botnet attempting to contact other devices for command-and-control. Adversaries are known to leverage it for command-and-control and defense evasion. Even if utilized by a legitimate user, it can circumvent some security controls.
PetitPotam Attack Via EFS RPC Calls
A device sent a Remote Procedure Call (RPC) using the Encrypting File System Remote Protocol (EFSRPC) Protocol library. The PetitPotam attack is known to be related to this type of RPC traffic. PetitPotam is a tool that can exploit this library. It is also known as an NTLM relay attack. Since most organizations don’t use this library at all, or limit the usage of it, any use is uncommon enough to indicate a possible PetitPotam attack.
Possible Impacket SecretDump Activity
A device is attempting a secrets dump using an impact tool such as secretdump.py, which allows dumping credentials from an Active Directory (AD) server. This is also referred to as a secrets-dump HKTL.
Remote Task Creation via ATSVC Named Pipe
A device is attempting to create a remote task using ATSVC named pipes, which could be a malicious attempt to use at.exe for performing task scheduling for initial or recurring execution of malicious code. The at.exe utility has been deprecated in current versions of Windows in favor of schticks.
Suspicious PsExec Execution
A device other than a Windows Sysinternal device is using psexec with a renamed service name, which could indicate a threat actor attempting to perform a remote execution.
Conclusion
Users of the Secure Network Analytics Data Store with Analytics will want to upgrade their instance to version 7.5.2 to gain access to nine new detections – four based on Network Visibility Module telemetry and five based on Zeek logs. These new detections are immediately available in Analytics. Configure the sources to export and expand your detection coverage today.
References
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Security Social Channels
Instagram
Facebook
Twitter
LinkedIn
Share:

